When it comes to your company’s network security, there are many common vulnerabilities that should be prioritized in order to protect your valuable assets. You can start by asking yourself a few questions about your business’ IT Security, specifically the protection of your data, work product, and productivity software to determine just how vulnerable you are:
- Do you keep everything up in the cloud?
- Do your employees carry those tiny USB sticks that can hold gigabytes of your data and be transported right out of your office?
- Have you assessed your overall risk?
- Is your data confidential in any way?
- Would your clients leave you if you got hacked?
- What if your business were hit with ransomware, how long could you be down before it hurts your operation? Is your hardware safe?
Of course, these questions are only the tip of the iceberg as far as the IT security questions that you should be asking yourself. There are so many questions, so many risk assessments to make, so many resultant decisions to make after thinking this stuff through and the process never ends. It’s enough to overwhelm even the smartest among us, let alone us mere mortals who have to run businesses every day, or IT departments, or even just being the IT person that everyone goes to. A very natural inclination is to assume everything is going to be okay and hope that it just “works out.” Hope that Alice in accounting doesn’t click on that link that implants ransomware on your server forcing you to decide whether to pay the ransom. (Don’t by the way. Don’t pay it).
We are bombarded with information every day
According to Marc Kaplan, security expert & CTO of SENT, “We have become so accustomed to being blasted with so much information every day that we literally act on them in a way that we would with anything else. We treat them with the lowest level of security possible. It only takes one time clicking on something that we shouldn’t. The bad guys have to be right only once and we as people, just general people have to be right all the time. Statistically that’s impossible for all of us. We have our day jobs, we come to work in the morning try to get our work done. Focus on what we have at hand. At the same time we have somebody whose sole job is to try and get into our system, whether it’s to put cryptocurrency miners into our laptop or to get passwords simply to use drop service or literally to just be able to laterally move across an enterprise or a door front. It does not matter. The problem is that the battle for people is challenging because it happens pervasively every day.”
Therein lies a pretty big issue for us. We have other things to do, other decisions to make that are directly related to our industries, not just IT. Who has time? By the way, these issues are just as pervasive in larger organizations as they are in smaller ones.
There is no immunity just because you have resources
Kaplan goes on to say, “Across the spectrum, from very small mom and pop shops to governments to some of the largest ecommerce companies in the world, it’s impossible to have enough resources. Even the biggest corporations lack on the side of IT and typically that’s where human error comes into play. The problems are the same regardless of the size of the company, and the people that work in an enterprise environment are going to be the same people that would work in a small office. There is no difference between them.
So because we tend to be, by nature, overly trustworthy of what happens around us, there needs to be a balance. We can’t walk around paranoid about every site we visit but we also don’t want to totally put our heads in the sand when it comes to security. Like everything, there needs to be a healthy balance.” Kaplan shares the following as ways to be mindful everyday:
Assess your current state
What hardware and software do you have in place? Is it secure? What does that mean by the way? Consider your Internet router or firewall as a starting point. This is your company’s entry point to the Internet. It could also be the entry point for a bad actor to get in on to your network and devices, it’s your front door on the Internet. What should you look for? Did you change the default password? If not, stop everything you are doing, and go change that password to something strong, let your password manager pick one out for you.
Use a password manager
If you aren’t using a password manager, start today, it’s another great step towards being more security aware. Stop using the same password everywhere. Second, turn off UPNP, or universal plug and play. This horrible service exposes your internal devices to the outside world and can easily become a way to learn about your infrastructure or to get to internal devices. What it does is give your router permission to automatically forward all traffic over a specific port back to a device that requests it. For instance, if you have a plug and play mail server appliance, it could ask your router via UPNP to automatically forward any and all email traffic to itself. This is crazy dangerous since you don’t know it’s happening and you are essentially leaving the door open. If you need to forward Internet traffic to your internal devices, then configure it manually so you have control over how it works and can turn it off when you want. There are enough exploits out there that take advantage of UPNP that warrant shutting it off.
Turn off external management of the gateway
What that means is that you can type in the public IP address of the router from a web browser and access the configuration screens. If it’s available to you, it’s also available to anyone else, unless your router or firewall allows you to limit access from specific IP sources. This is better, but it’s not ideal. There are more secure ways. If you didn’t setup or maintain your router, then it’s possible your IT person did that, mostly out of convenience. If it’s on, turn it off now. Anything that gives a signal to a bad actor of what hardware you are running or access to services, let alone access to configure your router, should be turned off unless you can give a really good reason to keep that front door open. If it’s about convenience, stop it.
Setup a VPN connection
Setup a VPN connection so that you can securely connect to the office and then manage the devices via a VPN. Does your router allow access rules? Most business class routers and firewalls will support this. Make sure it has a catch-all deny rule. If it does have rules, when did you last check those rules? If you rely on your ISP’s router like Verizon FIOS or Spectrum or someone like that, get the credentials and check the configuration. Make sure games, web pages and email are not allowed IN to your network. In general, unless you are hosting a public server from your network, then nothing should be allowed into your network, nothing. These are a small sample of things you can look at right away to help close the door and keep the bad guys from accessing your network.
Consistently be mindful
Being mindful means knowing that something needs attention and determining the best way to go about resolving any issues that come from those thoughts. Don’t assume that your IT department is handling it just because security is important. They might not know how or they might not have the budget to get the training or the tools they need. Setup a meeting with your IT department, consultant or in-house guru and discuss it. List out what matters to you, focus on that and then move on to the next thing. Without question, more will come up in the natural course of addressing these issues.
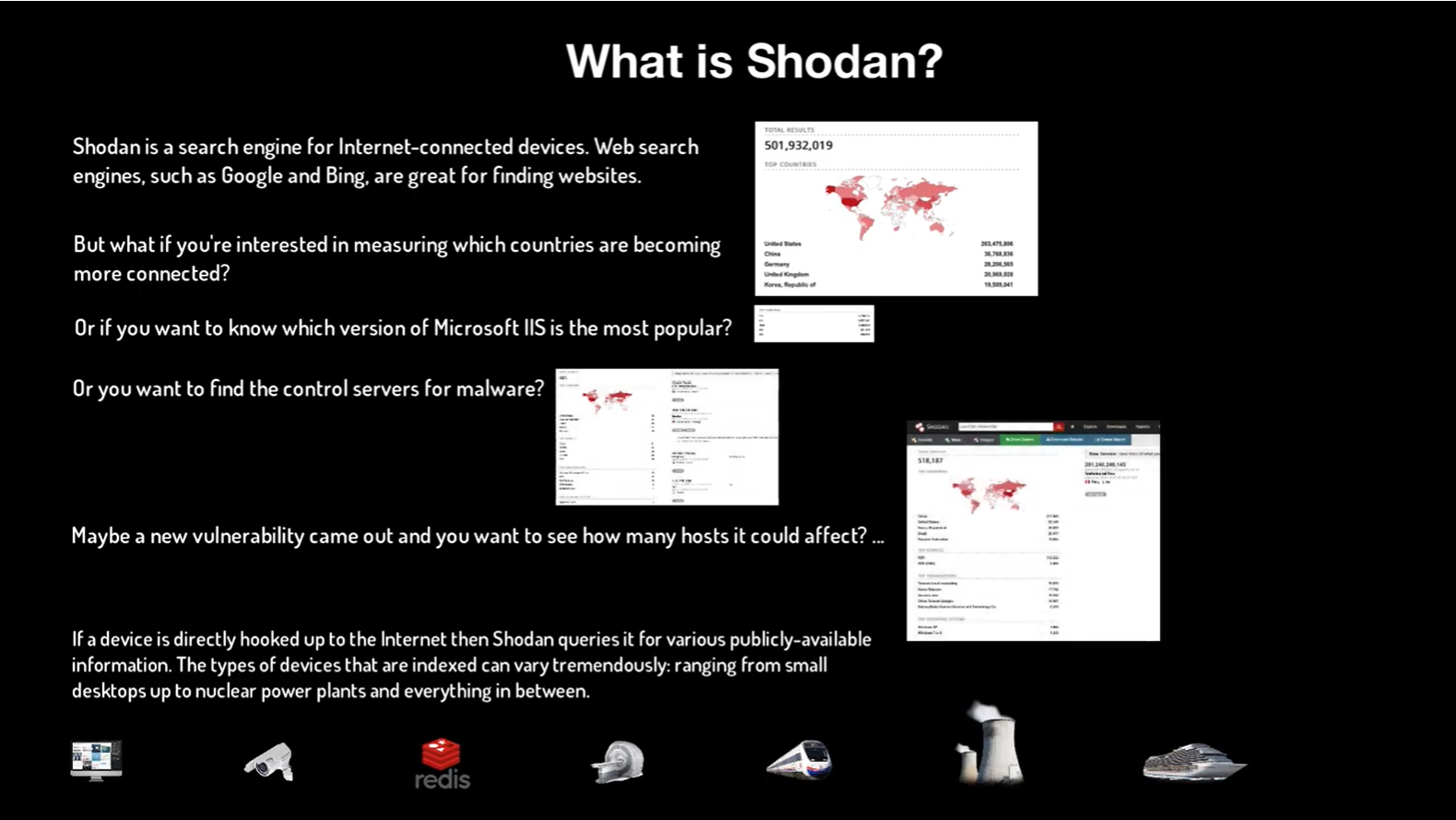
Keep your head up for known vulnerabilities, exploits and fixes
The big hacks that get into the news are good to know about and should inform your priorities when discussing your security status, but the devil is in the details, quite literally. The US Homeland Security department operates a web site called US CERT, for Computer Readiness Emergency Readiness Team. You can subscribe for free to alerts about updates, vulnerabilities and issues to be on the lookout for. For instance, during tax season they send out guides on how to protect your financial information. It’s a great resource to stay aware.
It’s never too soon to start thinking about IT security and your own needs and concerns. Taking this actionable and practical steps can help you feel more confident in your IT systems.
Related Posts:
Manufacturer & Software Companies aren’t Taking Care of Security For You
Enterprise Security: It applies to small and medium sized businesses